Forensics
How many times have you needed to go back in time to investigate or prove that a certain situation happened?
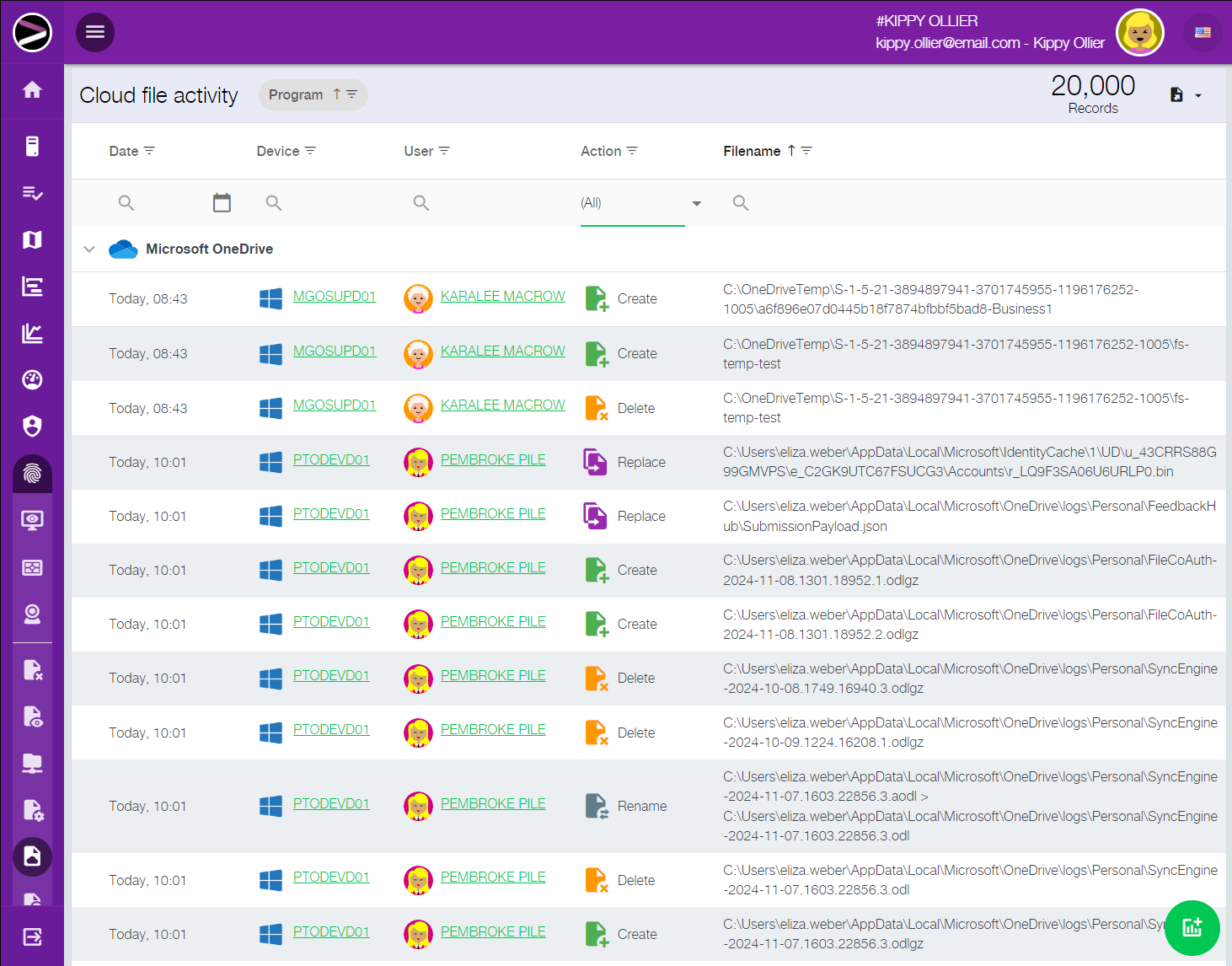
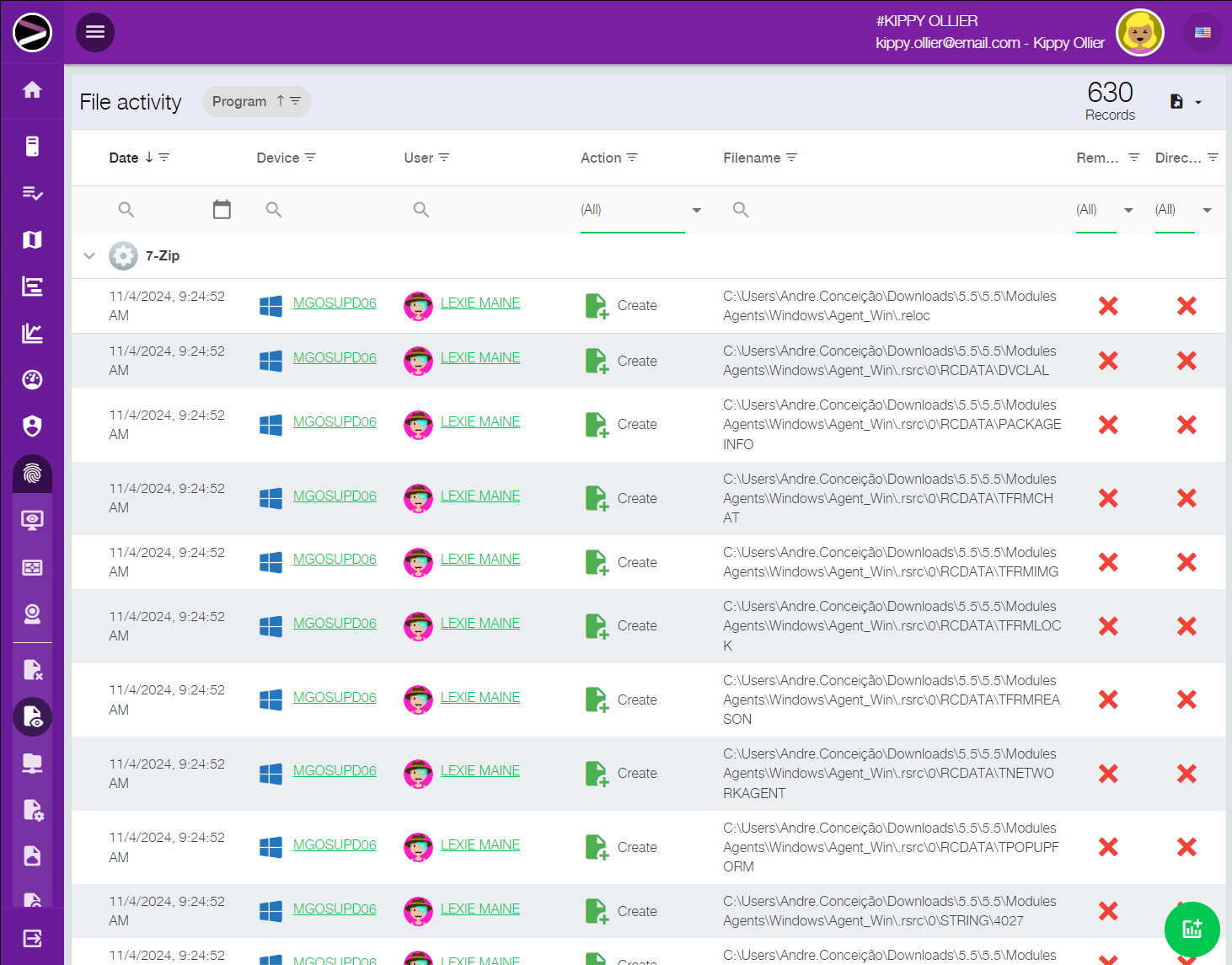
Do you have access to any activity in the cloud? iCloud / Dropbox / Google Drive / OneDrive / Box
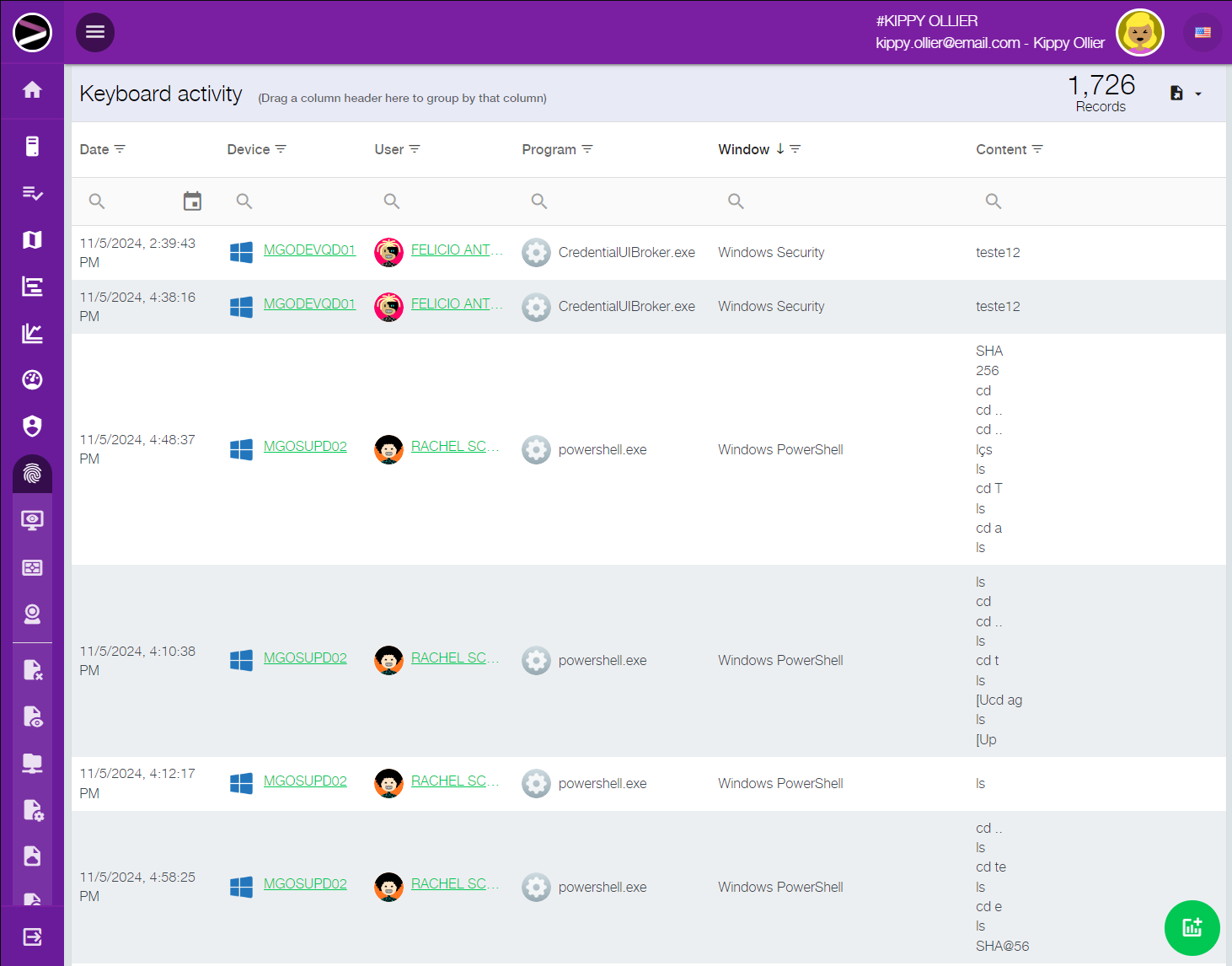
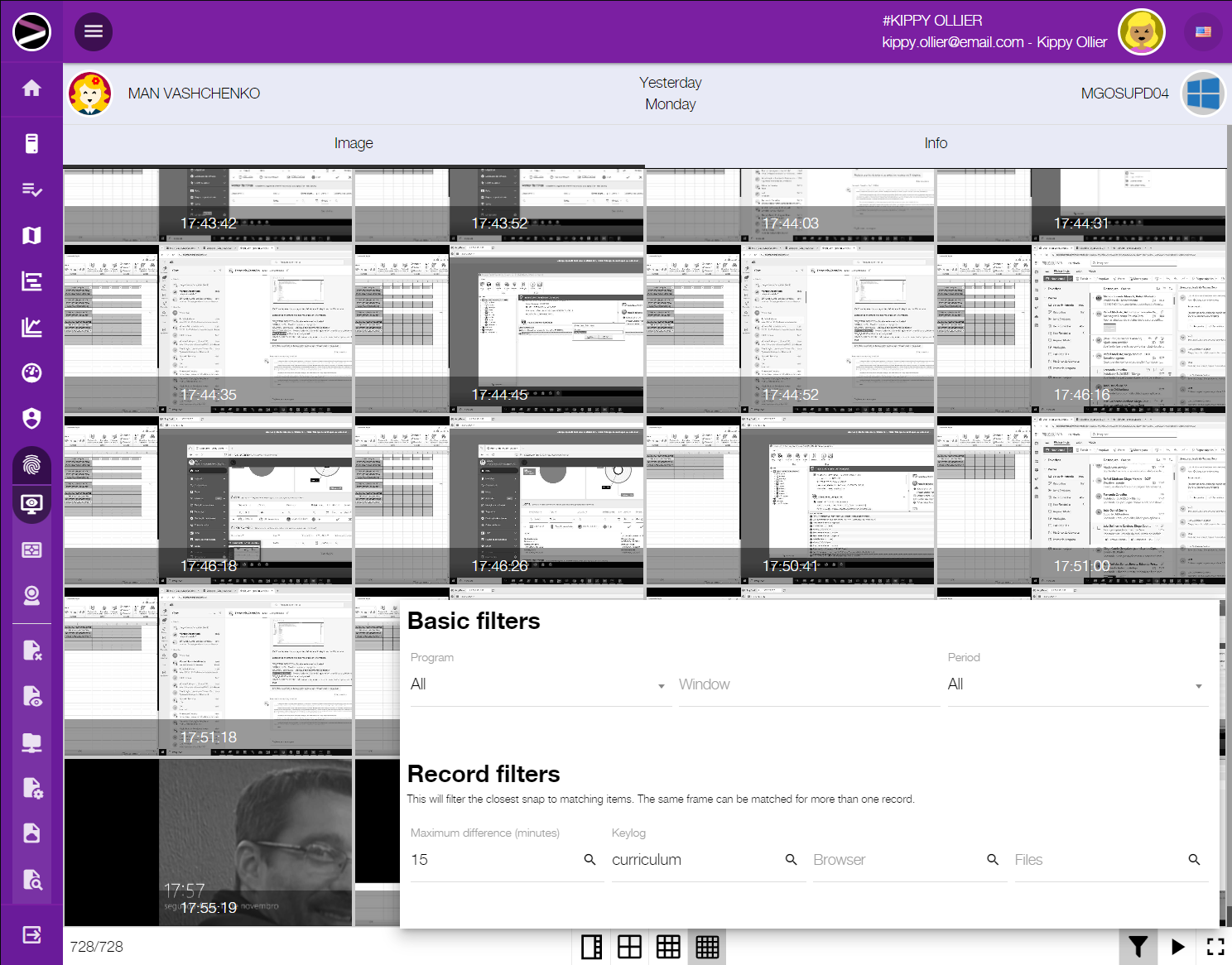
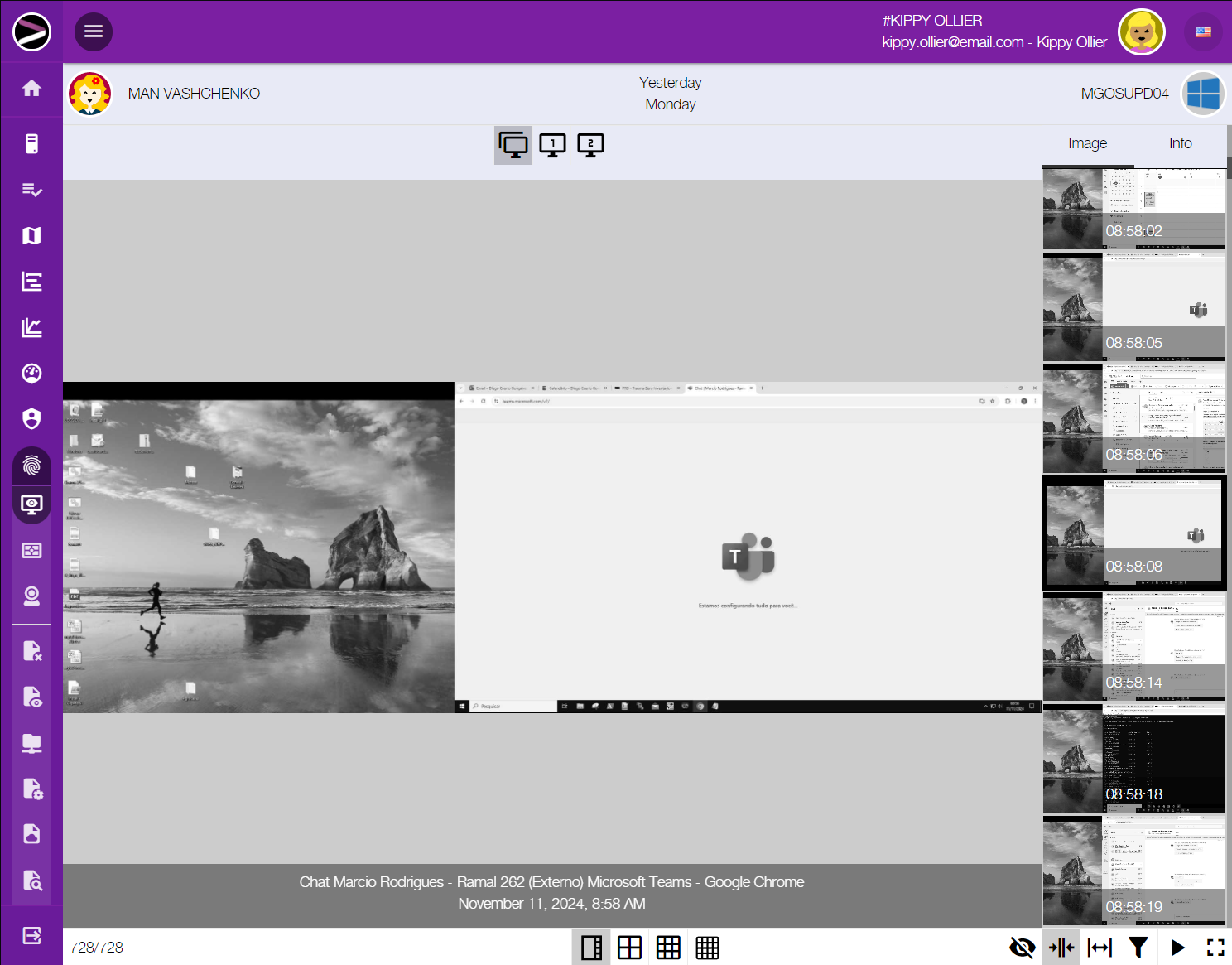
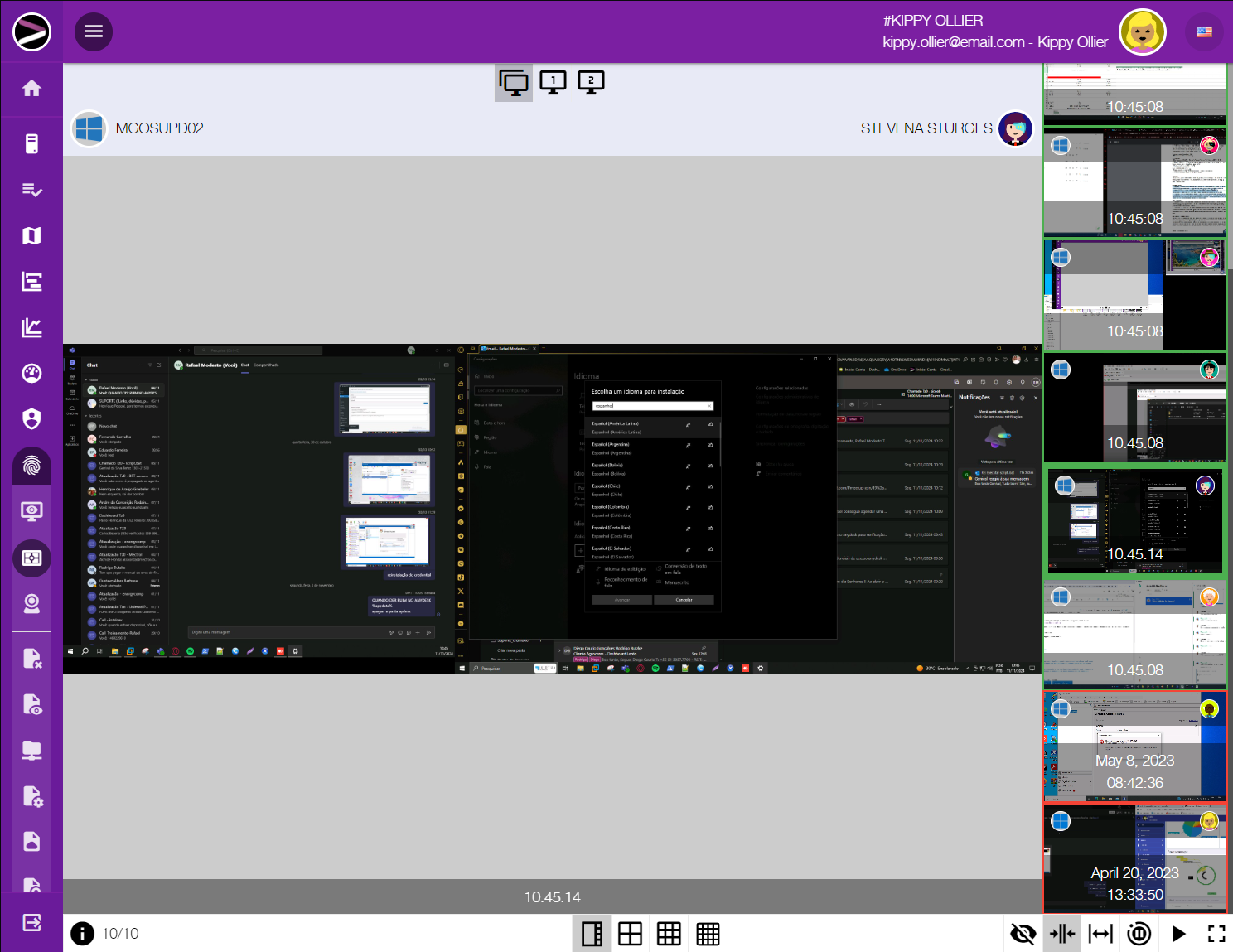
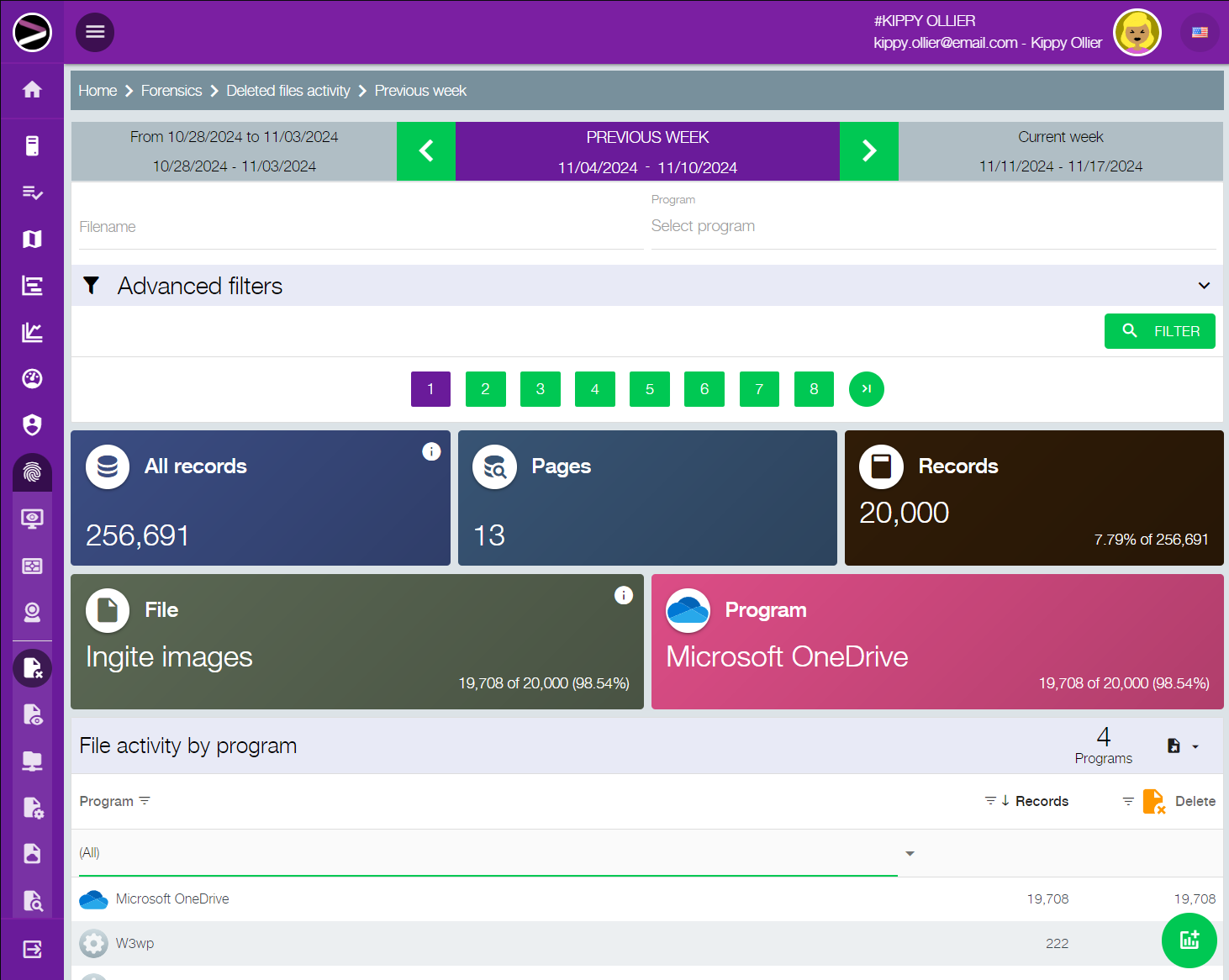
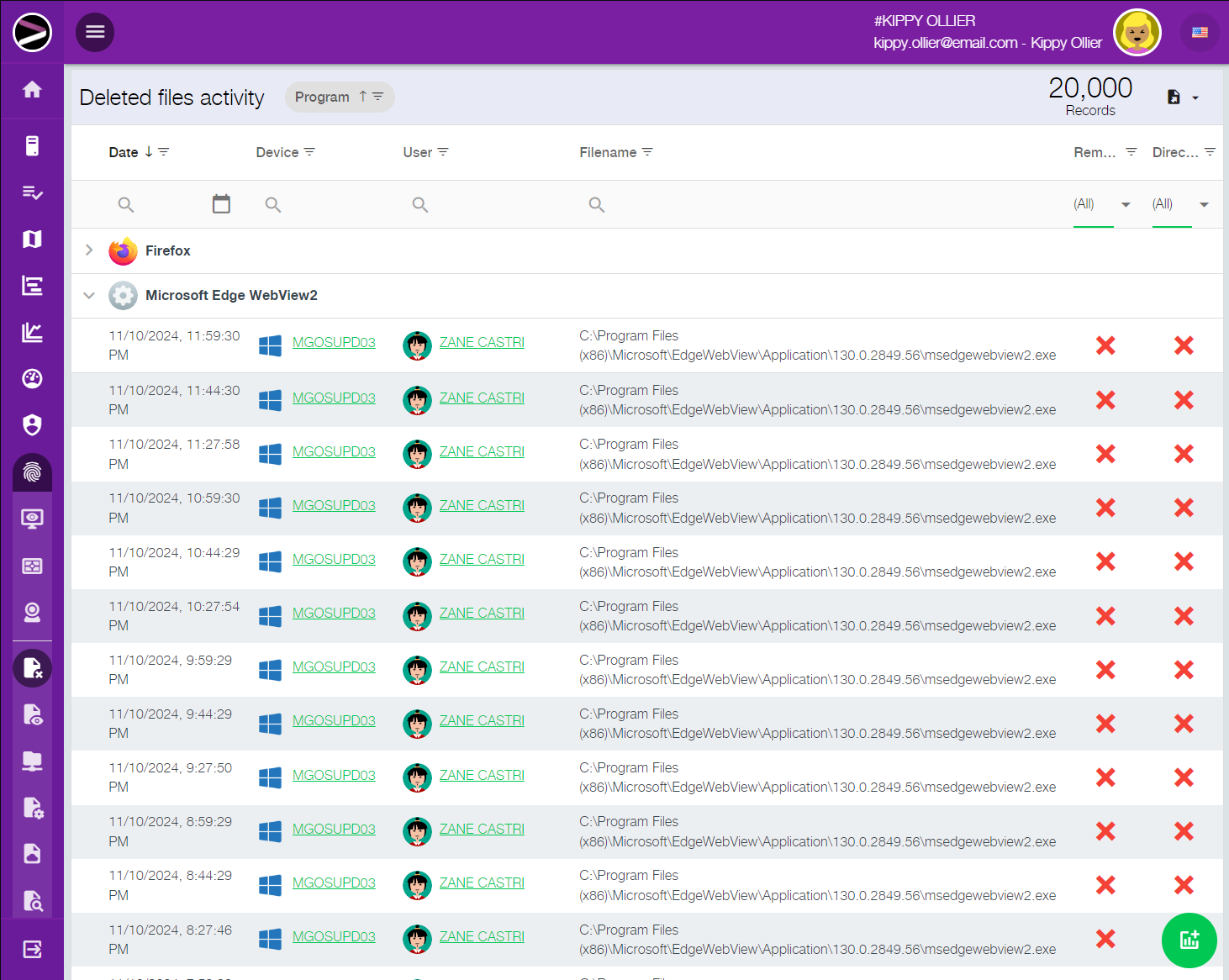
Do you need to search for something typed by a colleague, or even access everything someone typed on a specific date? Do you need to know all the websites visited, the browsers used, the time period, and which user or device was used? A certain file disappeared from the network; you need to investigate how, when, by whom, and why?
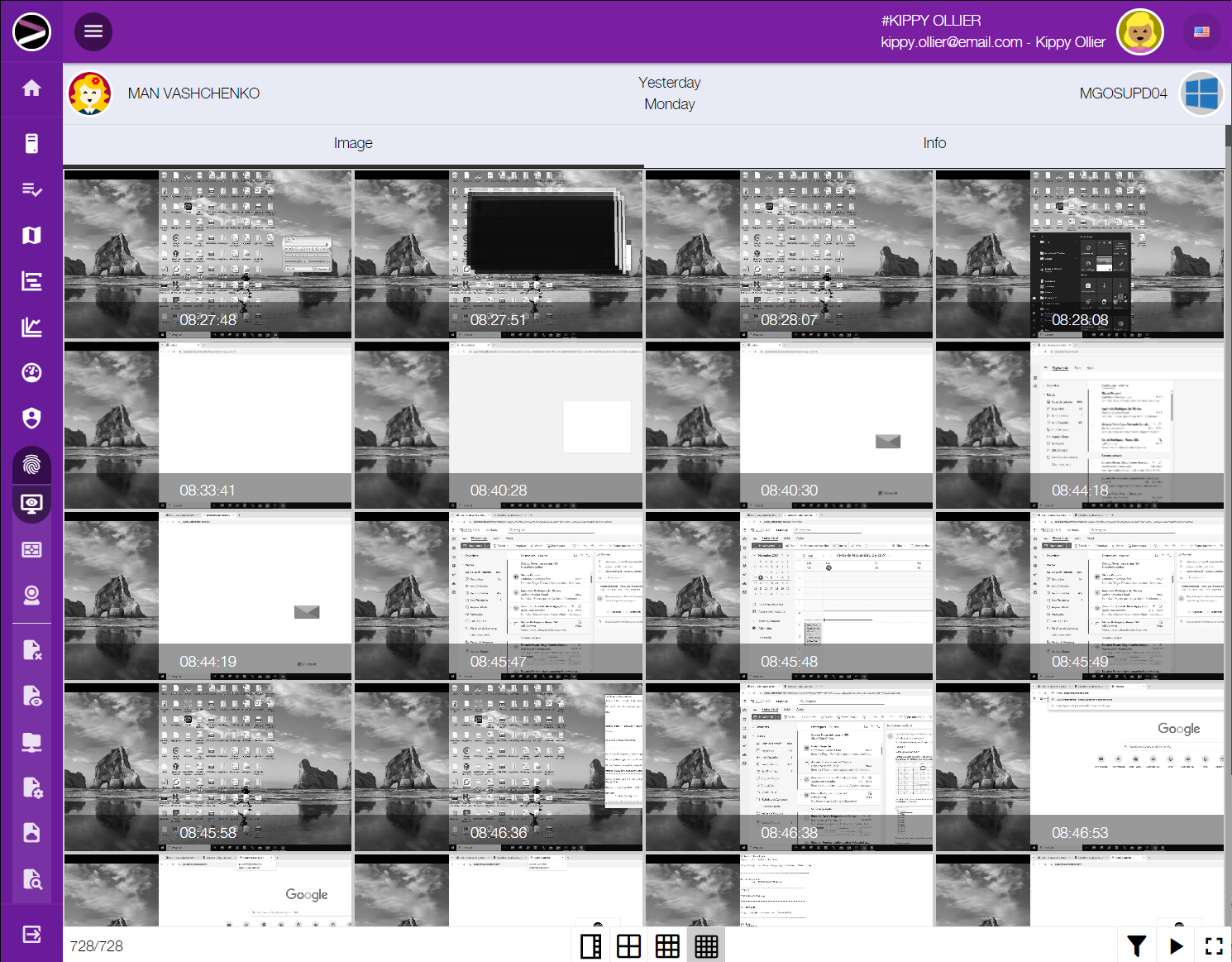
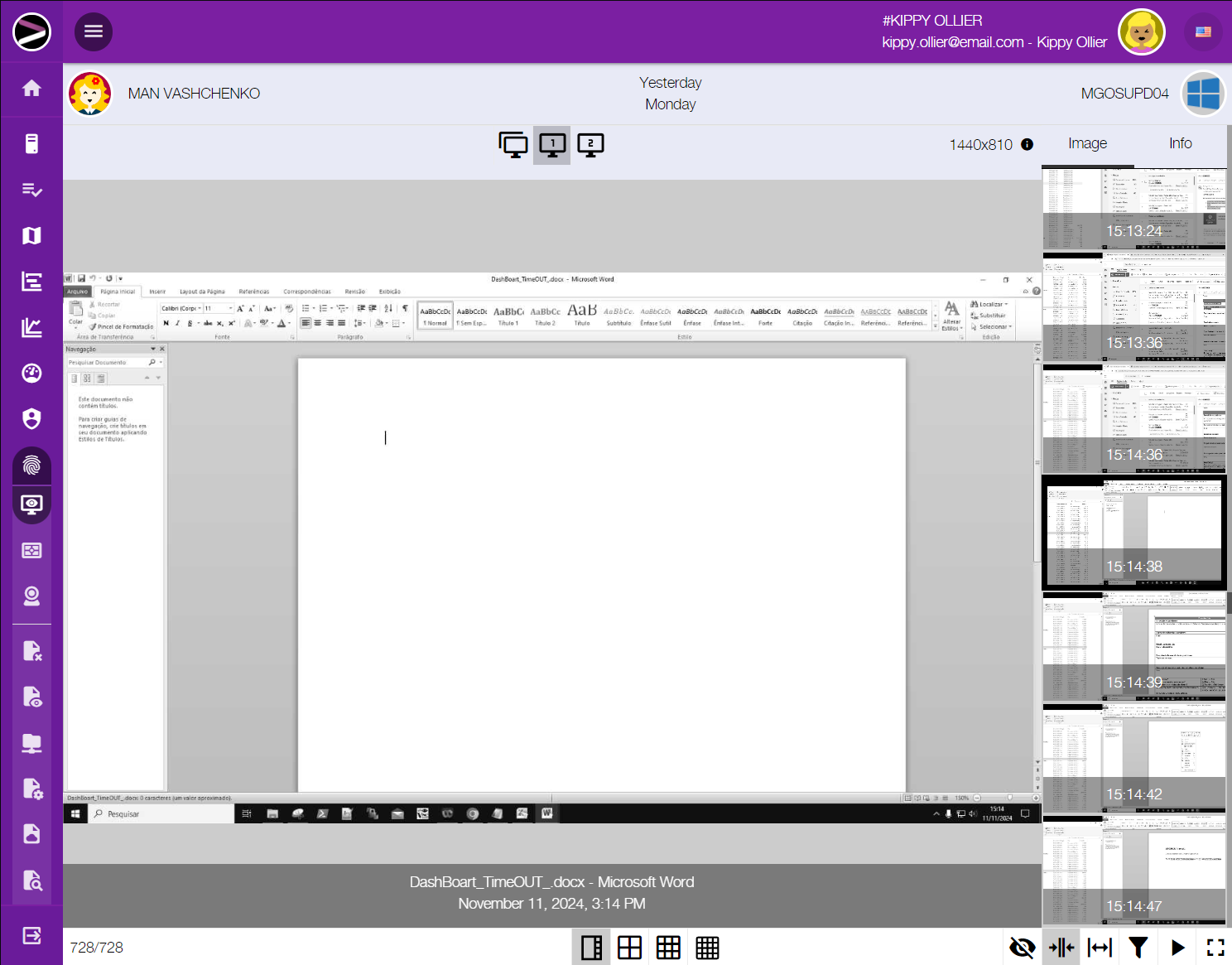
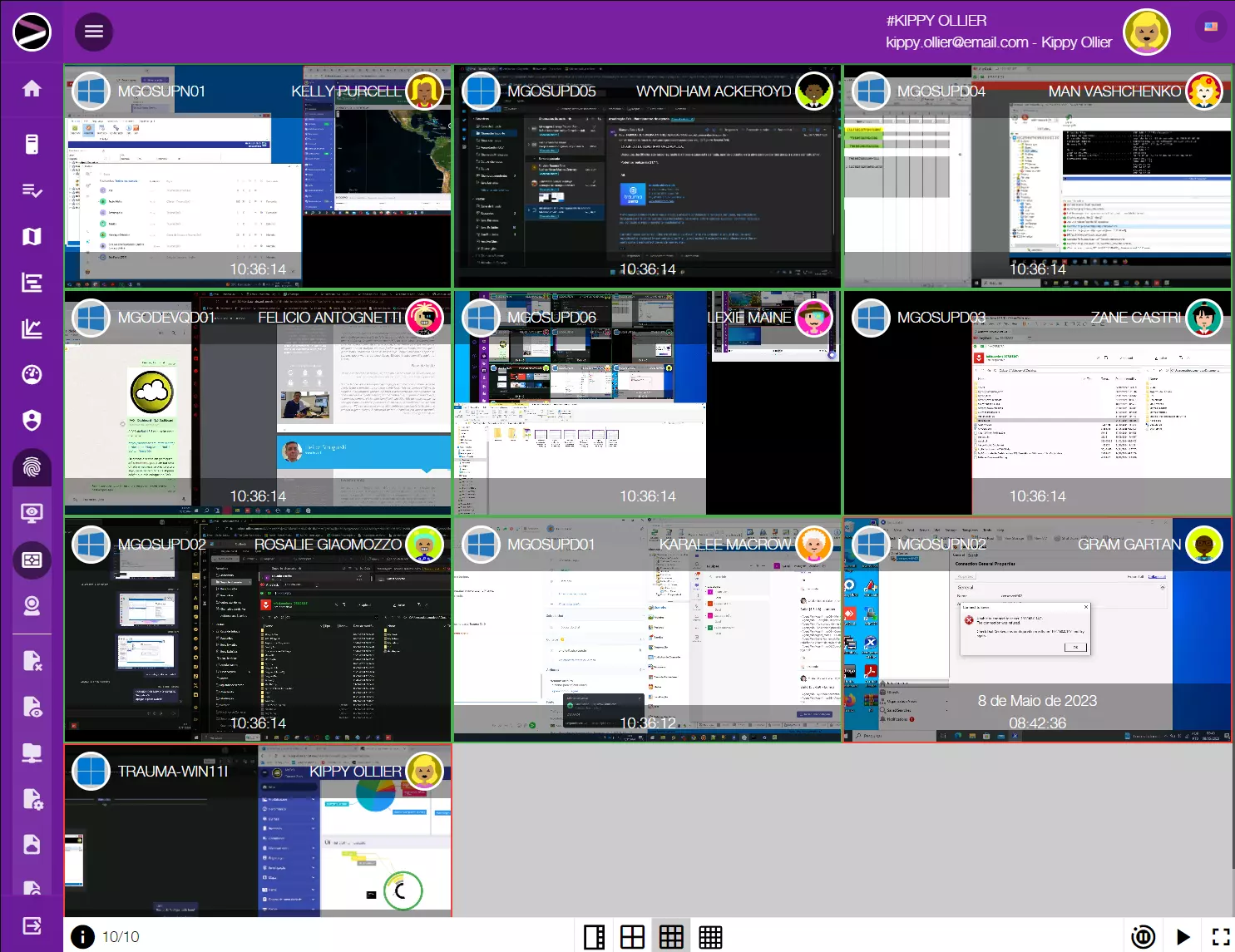
We've combined 20 years of experience and all our most immersive investigative technology into the Forensics product. We consider nothing less than allowing you to go back in time, enabling you to analyze every detail of what happened on your company's network, second by second, all the visual activity of what occurred on the devices.

Threat Tracking
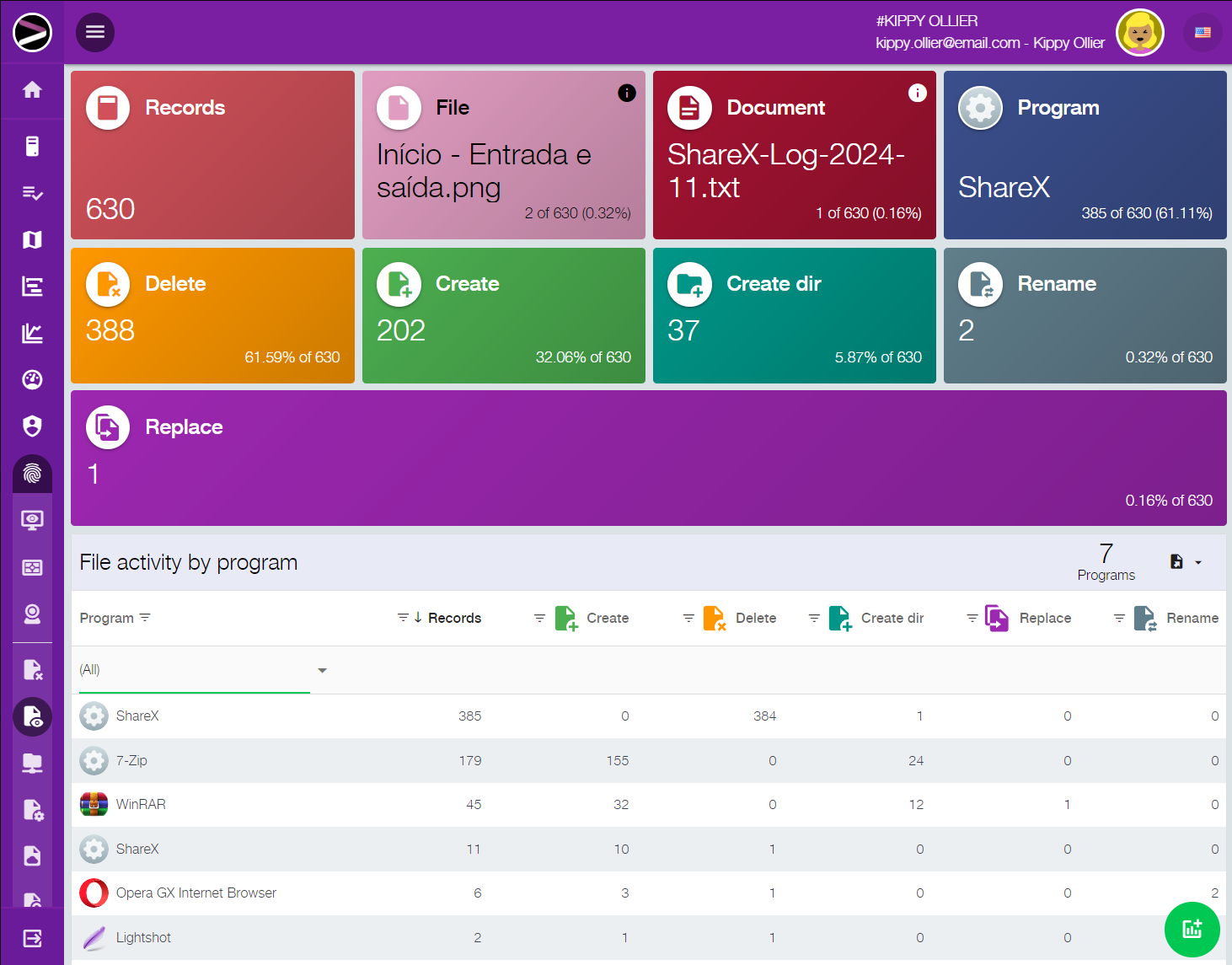
Track suspicious activity in your technology environment.
Legal Reports and Evidence
Issuance of technical reports to assist in legal matters, which may include evidence used in legal proceedings.
Data Loss Protection
Reduce losses due to the misuse and/or exclusion of strategic information.
Silent and Remote Operation
It works silently, transparently, and remotely, storing the history in a database.
Trigger Monitoring
Monitoring can be triggered by actions performed by the user.
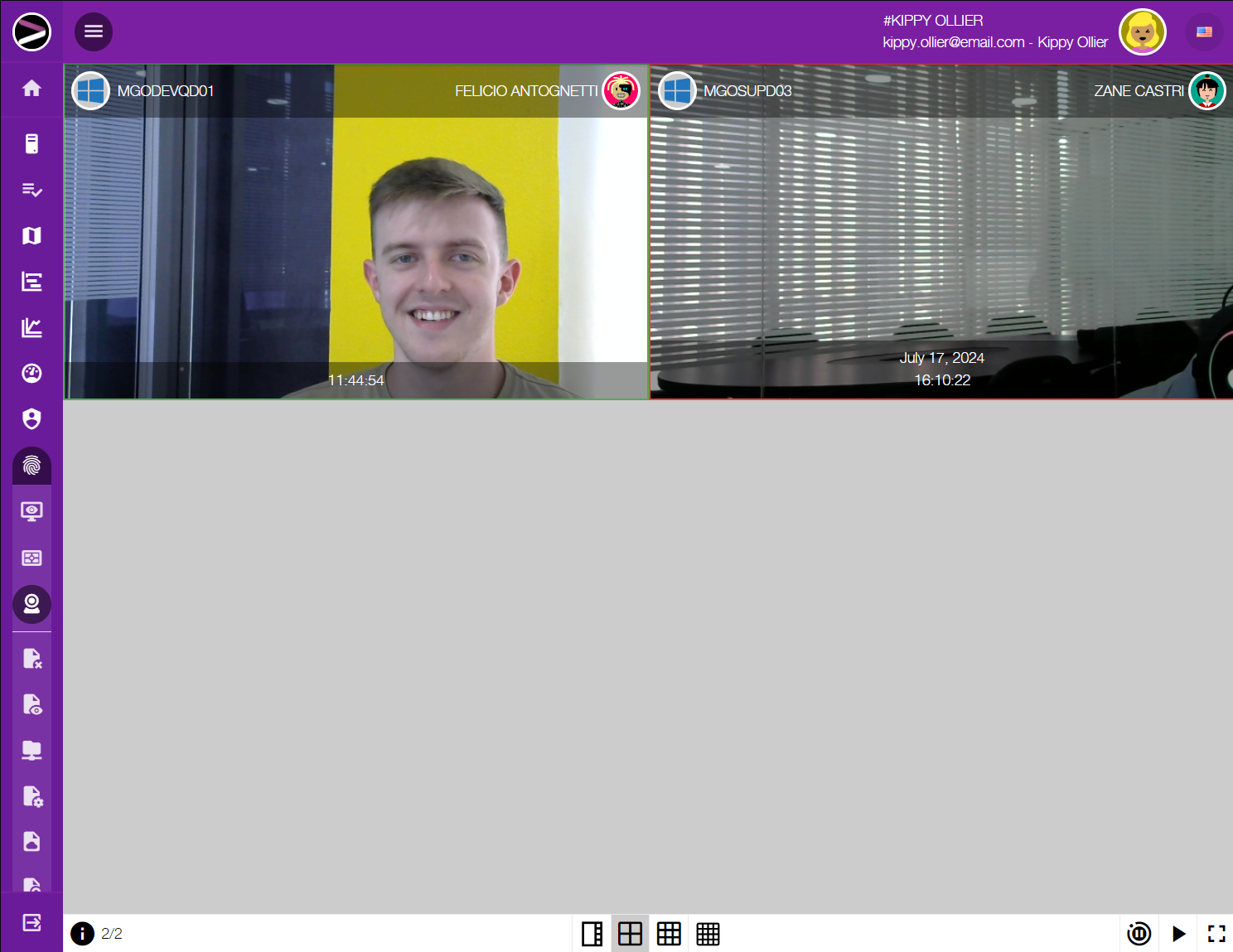
Total Activity Capture
It monitors all user actions on the device, capturing all resources.
This is just part of the arsenal of resources we are offering you to enable your company to have a time machine at its disposal, allowing it to have all the answers to all the questions that your complex IT environment may require, as well as giving you guarantees for adverse situations that the new LGPD law may require.
Product gallery